Modern digital lifestyles require technology that delivers dependable results every day. Durable computing devices have become essential for professionals, students, businesses, and home users who value long lasting performance and reliability. From handling office work to supporting creative projects and online learning, high quality computing systems are designed to provide stable performance for years while maintaining efficiency and productivity.
Why Durability Matters in Modern Computing
Reliable computing devices are built to support continuous daily use without sacrificing speed or functionality. Long lasting systems help users avoid frequent replacements, reduce maintenance concerns, and improve overall workflow efficiency. Durable devices are especially valuable for remote workers, growing businesses, and students who rely on technology for communication, collaboration, and task management.
Key benefits of durable computing devices include:
- Extended operational lifespan
- Stable performance during multitasking
- Reduced long term technology expenses
- Better reliability for daily productivity
- Consistent support for professional applications
These advantages make durable computing solutions an excellent investment for users seeking both performance and value.
Features That Support Long Lasting Performance
Modern computing devices are designed with features that promote reliability and smooth operation over time. Efficient hardware, strong build quality, and optimized system performance all contribute to long term usability.
Important features commonly found in dependable devices include:
- Fast and responsive processing capabilities
- Efficient cooling systems for continuous use
- Energy saving performance optimization
- Comfortable and user friendly designs
- Reliable storage solutions for important files
- Strong wireless connectivity for remote access
These features help users maintain productivity while ensuring that devices continue performing efficiently under regular workloads.
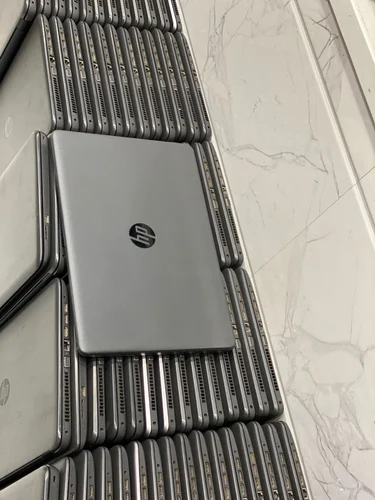
Ideal for Work, Education, and Everyday Use
Durable refurbished laptop windows 11 are suitable for a wide range of environments. Professionals benefit from reliable performance during video meetings, presentations, and multitasking. Students can complete online classes, research, and assignments with confidence. Home users also enjoy smoother browsing, entertainment, and digital communication experiences.
Popular uses for durable computing devices include:
- Remote work and virtual collaboration
- Online education and digital learning
- Creative projects and content creation
- Data management and document storage
- Daily productivity and communication tasks
Because of their versatility, durable devices continue to support both personal and professional growth.
Cost Effective and Sustainable Technology Solutions
Long lasting computing devices provide excellent long term value by reducing replacement frequency and minimizing maintenance costs. Many users now prioritize durable technology because it combines affordability, efficiency, and sustainability. Devices that remain reliable for extended periods also contribute to environmentally responsible technology usage.
Advantages of investing in durable technology include:
- Lower overall ownership costs
- Reduced electronic waste
- Better energy efficiency
- Consistent long term productivity
- Improved return on technology investment
These benefits make dependable computing devices a smart choice for individuals and organizations focused on sustainable growth.
Conclusion
Durable computing devices play an important role in supporting modern productivity and digital lifestyles. Their long lasting performance, reliable functionality, and efficient operation make them valuable tools for work, education, and everyday activities. With practical features, dependable performance, and strong long term value, durable computing solutions continue to meet the growing demands of today’s connected world. Investing in reliable technology helps users stay productive, organized, and prepared for future digital challenges.






